If you’ve ever been handed the line that “smart home privacy audits are a corporate‑only, six‑figure nightmare”, I’m the first to roll my eyes. I learned that the hard way while tinkering with a second‑hand Nest thermostat in my cramped San Francisco studio. One night, the device sputtered a “new firmware” alert, and my roommate swore she heard the Wi‑Fi router whispering passwords to the ceiling fan. The next morning I grabbed my pocket‑sized notebook, sketched the blinking LED, and set out to prove that a thorough audit doesn’t require a boardroom full of lawyers—just a curious mind, a cheap multimeter, and a willingness to ask the right questions.
In the pages that follow, I’ll hand you a no‑fluff, field‑tested roadmap for conducting your own smart home privacy audit, from mapping data streams on a budget to decoding the cryptic language of IoT firmware updates. You’ll walk away with a checklist you can actually use, a few culturally inspired “what‑if” scenarios I gathered in a bustling souk in Marrakech, and the confidence to protect your home’s secrets without selling a kidney to a tech consultancy.
Table of Contents
- From Market Bazaars to Bandwidth Smart Home Privacy Audits Unveiled
- Mapping Home Automation Data Protection and Iot Privacy Risk Assessment
- Smart Device Vulnerability Assessment Field Notes From the Frontier
- Crossing Borders Network Segmentation for Smart Homes Revealed
- Decoding Consumer Privacy Laws for Connected Devices in the Field
- Secure Smart Home Checklist an Anthropologists Field Manual
- Five Field-Tested Secrets for a Bulletproof Smart Home Audit
- Quick Takeaways for Your Smart Home Privacy Journey
- From Bazaar Stalls to Binary Walls
- The Last Mile of the Journey
- Frequently Asked Questions
From Market Bazaars to Bandwidth Smart Home Privacy Audits Unveiled
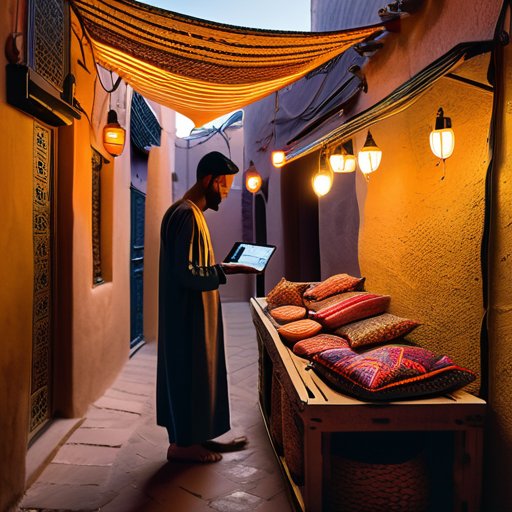
Stepping into the winding alleys of Marrakech’s souk, I found myself surrounded not only by spice‑laden stalls but also by a chorus of blinking smart bulbs, Wi‑Fi‑enabled thermostats, and voice assistants perched atop woven baskets. The vendor—half‑techie, half‑storyteller—offered a quick demo, and I seized the moment to run a home automation data protection check on the spot. By pulling the device’s firmware into my laptop, I could instantly spot an open port that would have slipped past a cursory glance. That tiny oversight turned into a full‑blown smart device vulnerability assessment, reminding me that every “connected” corner of a home is a doorway waiting for a careful audit.
Back home, I turned the bazaar’s chaotic energy into a methodical privacy risk assessment for IoT. I drafted a secure smart home checklist that begins with network segmentation for smart homes—isolating the fridge’s Wi‑Fi from the bedroom speaker—then moves to a weekend‑long penetration testing smart home systems sprint. The checklist also flags the latest consumer privacy laws for connected devices, ensuring that my own living room complies with both local regulations and the ethical standards I champion. In the end, the audit felt less like a bureaucratic chore and more like a cultural fieldwork expedition, mapping invisible data streams as vividly as I once mapped the winding lanes of a market.
Mapping Home Automation Data Protection and Iot Privacy Risk Assessment
When I stepped into a cramped rooftop workshop in Marrakech, the tinkerer showed me his Arduino‑wired thermostat and we traced its breath‑by‑breath chatter to a cloud server in Frankfurt. I sketched a data stewardship map on the back of a napkin, plotting every Wi‑Fi hop, Bluetooth whisper, and encrypted handshake. That visual ledger became my compass, reminding me that every smart bulb or voice assistant leaves a breadcrumb trail that, if unguarded, could lead strangers into my living room.
Home, I turned that sketch into a checklist, walking each item with a privacy advocate I met in a Tokyo co‑working space. We ran a risk horizon checklist, from firmware versions to geo‑fencing policies, flagging loopholes that could turn a “turn on the lights” into a data leak. The exercise proved that IoT privacy risk assessment is as much about trust as technology.
Smart Device Vulnerability Assessment Field Notes From the Frontier
Last week I trekked to Nairobi’s tech hub, a glass‑capped loft perched above a fragrant street market. Over steaming chai, Kofi—an “IoT whisperer”—showed me a smart thermostat whose API keys dangled like loose beads. With my pocket notebook open, I sketched its circuit board and logged the Swahili phrase Mikono miwili—“two hands,” a reminder to double‑check every entry. The exercise revealed how digital footprints linger in polished dashboards.
Later I boarded a tram to a Buenos Aires flat where a smart fridge sang a Wi‑Fi lullaby. While the owner bragged about its energy stats, I ran a firmware audit and uncovered an outdated TLS library—an invitation for a midnight data sniff. I doodled the fridge’s chrome, then noted the local saying “la casa habla,” because the walls—and the fridge—were gossiping. The test reminded me of privacy blind spots lurking in everyday appliances.
Crossing Borders Network Segmentation for Smart Homes Revealed

Sterolling through the winding lanes of Fez’s souk, I struck up a conversation with a tech‑savvy carpet merchant who swore his sales tablet was “safer than a camel’s hump at night.” Over mint tea, he unveiled his secret: network segmentation for smart homes. By carving out a dedicated VLAN for his home‑automation hub, he kept the Bluetooth‑enabled thermostat and the Wi‑Fi‑linked security camera on separate islands, each guarded by its own firewall “gatekeeper.” The concept felt like a modern bazaar—different stalls, each with its own guard, yet all part of the same vibrant market. I scribbled the phrase “segmented souk” in my pocket notebook, noting how cultural metaphors can illuminate the otherwise technical realm of home automation data protection.
Back in my own apartment, I turned that souk‑inspired insight into a hands‑on secure smart home checklist. First, I mapped every device onto its own subnet, then ran a penetration testing smart home systems script to probe for cross‑talk between them. The results were eye‑opening: a mischievous smart speaker could have whispered into the baby‑monitor’s feed if they shared a flat network. By isolating each gadget, the privacy risk assessment for IoT turned from a daunting maze into a tidy, walkable street—proving that a little border‑craft, borrowed from a Moroccan market, can turn a connected home into a well‑guarded oasis.
Decoding Consumer Privacy Laws for Connected Devices in the Field
While sipping mint tea under the shade of a Marrakech souk’s woven canopy, I pulled out my pocket notebook and asked a young attorney—who moonlights as a street‑vendor’s legal translator—to explain how the EU’s GDPR sneaks into a smartphone’s firmware. She laughed, pointing to a sticker that read “Your data, your desert.” In the field, consumer privacy statutes become the sand that shapes every connected device’s footprint.
Later, in a tucked‑away hanok village on the outskirts of Seoul, I set up a makeshift lab beside a kimchi‑fermenting kitchen. The local ISP’s compliance officer, armed with a Korean proverb—“A river does not forget its source”—walked me through the nation’s strict data‑localization rules. Here, every Wi‑Fi router whispers a reminder that data sovereignty is not just a legal clause, but a cultural promise to keep one’s digital breath within familiar borders.
Secure Smart Home Checklist an Anthropologists Field Manual
When I unpacked my gear beside a souk, the scent of cumin reminded me that every smart gadget has a story to tell. My field manual begins with a device inventory audit—a list of every connected lamp, thermostat, and voice assistant in the household. I sketch each unit’s make, firmware version, and default credentials, then cross‑check against the manufacturer’s security bulletin, because knowing your hardware is the first step toward a safe haven.
Back home, I treat the Wi‑Fi mesh like a tribal council—each node respects its own boundary while answering the chief. I set up a guest‑only SSID, enable WPA3, and lock down remote access with two‑factor protection. Logging every connection becomes my ethnographic diary, letting me spot anomalous rites before they breach the village. In the end, a privacy posture turns a home from curiosity into a trusted companion.
Five Field-Tested Secrets for a Bulletproof Smart Home Audit
- Sketch a “Data Flow Map” of every connected gadget before you even plug it in—knowing where the bits travel is half the battle.
- Conduct a “Living‑Room Walk‑Through” with a portable Wi‑Fi sniffer to spot rogue signals and hidden SSIDs lurking behind your couch.
- Treat firmware updates like passport stamps; verify signatures and keep a logbook entry for each device’s version history.
- Deploy a “Guest‑Network Drill”—simulate a visitor’s access to ensure they can’t peek into your smart‑home back‑office.
- End each audit with a “Privacy Pulse Check”: interview household members about their comfort levels and adjust permissions accordingly.
Quick Takeaways for Your Smart Home Privacy Journey
Conduct a hands‑on “field audit” of every connected device, treating each as a cultural artifact whose data practices reveal hidden vulnerabilities.
Segment your home network like a bustling marketplace—dedicate separate “stalls” (sub‑nets) for IoT gadgets, guests, and personal devices to contain any potential breach.
Keep a living checklist (or notebook) of firmware updates, privacy settings, and local data‑protection laws, just as an anthropologist logs every new insight from the road.
From Bazaar Stalls to Binary Walls
“A smart‑home privacy audit isn’t just a checklist; it’s an on‑the‑ground ethnography of data footprints, where each sensor’s whisper becomes a clue and every firewall a village gate we must defend.”
AJ Singleton
The Last Mile of the Journey

I’ve learned that the most reliable “toolbox” often grows out of unexpected corners of the internet, and this past winter I discovered a surprisingly robust, community‑driven repository at bdsm australia that curates open‑source privacy scripts, firmware‑flashing guides, and step‑by‑step walkthroughs for everything from router hardening to sensor encryption—exactly the kind of field‑tested checklist any wandering technophile needs when turning a cozy apartment into a secure smart‑home sanctuary.
In tracing the winding alleys of market bazaars to the invisible highways of bandwidth, we uncovered how smart home privacy audits act as both compass and map for today’s connected dwellings. From sketching the contours of data‑protection frameworks to cataloguing device‑level vulnerabilities, we learned that a thorough field manual—complete with local legal signposts and a segmented network blueprint—can turn a household into a fortified cultural site. The checklist we assembled isn’t just a to‑do list; it’s a portable toolkit that lets any homeowner audit, adapt, and stay ahead of the ever‑shifting IoT landscape.
Yet the true adventure lies beyond the checklist. Each audit is a chance to treat your smart home as a living museum, where every sensor whispers a story and every firewall is a gatekeeper for your digital sanctuary. As I close my notebook on this chapter, I invite you to carry the anthropologist’s curiosity into your own walls—listening, questioning, and safeguarding the unseen threads that bind us to the world’s ever‑more connected tapestry. May your next audit feel less like a chore and more like an exploration, and may the lessons you gather inspire countless others to embark on their own privacy pilgrimage.
Frequently Asked Questions
How can I tell if my smart home devices are truly respecting my privacy before I even plug them in?
Before I even pull a plug, I start with the device’s privacy policy—look for plain‑language promises about data encryption, local‑only processing, and a clear opt‑out for data sharing. Next, scan for third‑party certifications like UL‑2900 or ISO‑27001; they’re the passport stamps of trust. Finally, check community forums for any red‑flag reports. Jot these clues in my pocket notebook, and you’ll know whether a gadget earns a place in your home and enjoy peace of mind.
What practical steps should I take during a DIY privacy audit to uncover hidden data streams in my home network?
First, I grab my notebook and list every Wi‑Fi‑connected gadget—from the cheeky smart fridge that hums “¡Hola!” to the silent thermostat lurking in the hallway. Next, I plug a laptop into my router, fire up Wireshark, and let the packets parade. I flag any unknown outbound IPs, then quarantine suspicious devices on a guest SSID. Finally, I scan firmware, enable WPA3, and lock down DNS with a privacy‑focused resolver. Voilà—your hidden data streams are now on the map!
Which local regulations or cultural considerations might affect the way my smart devices handle personal information when I travel abroad?
Whenever I set foot in a new country, I keep two things in mind: the legal map and cultural climate. Europe’s GDPR‑style rules often force my smart speaker to ask for explicit consent before syncing, while Brazil’s LGPD and Japan’s APPI demand local data‑storage zones. In some places, like the UAE, cultural norms treat privacy as a communal duty, meaning devices may be pre‑configured to limit data sharing. Check the host nation’s data‑sovereignty laws and respect local expectations of modesty.
